Nano 4G
Components
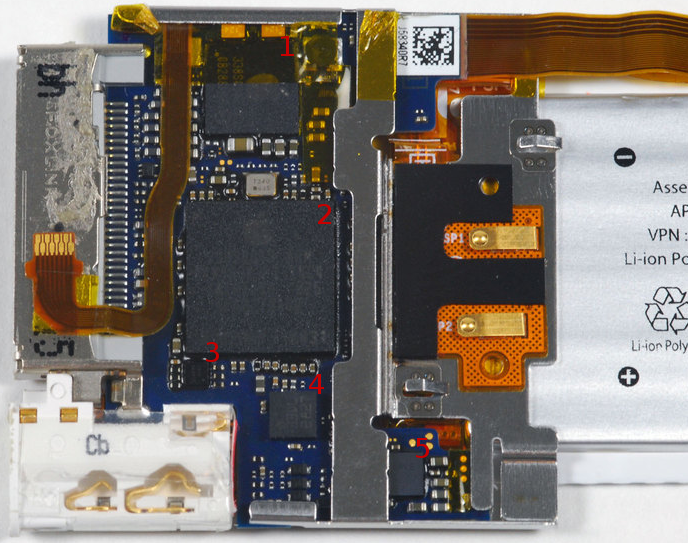
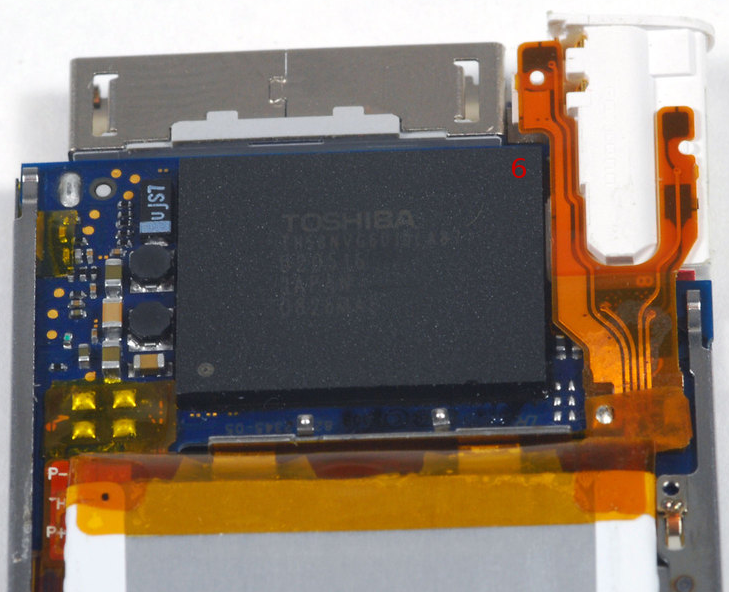
| Label | Component | Part | Markings | Notes |
|---|---|---|---|---|
| 2 | CPU | Samsung S5L8720 | 339S0049 ARM, K4X56323PI-KGC4, YWE025QH 825, APL0278A00, N1B2HOP 0831 | ARM1136JZF-S processor. It is definitely worth knowing that this is the exact same processor used in the iTouch 2G. This could mean that some of the same exploits for that could possibly be used. Here is a very interesting page about the S5L8720 processor. |
| SDRAM | 32MB, probably MDDR. Integrated into the processor, similar to the iPod Touch and iPhone lines. | |||
| 4 | Accelerometer | LIS331DL | 33DL, 2827 | The newer Touch's, iPhone's, and even the iPad have similar accelerometers, and I've discovered a pattern in the chip names. |
| 6 | NAND Flash | Varies | TH58NVG6D1DLA87, U20516, JAPAN, 0826MAE | |
| 5 | Audio codec | Probably Cirrus | 338S055C, 189N0824, SGP | I determined this because the Nano 5G has a similar chip, which we are sure of the identity. One person lifted this chip and found that the pins connect to the LCD connector. Not much info was given, and it could just be a common ground, but the identity of this chip is still up in the air. |
| 1 | Power manager | D1759 | 338S0687-AC, 08288HBB | |
| 3 |
Executing Code
As of now the only way to execute code on the nano 4g is through the Notes vulnerability and with Pwnage 2.0. As we don't know yet how to initialize the SDRAM on the nano 4g the only useful method is by using the Notes vulnerability. The only working note at the moment is an iBugger loader.
Attention: The Notes vulnerability was patched in the v1.0.4 firmware update of the nano 4g. You need to downgrade to v1.0.3 to still use the Notes vulnerability.
To run iBugger loader download the nano 4g iBugger package. To use the scripts in there you need a working Python Toolchain
Simply put the "n4g-ibugger.bootnote" in the "Notes" directory of your iPod and safely remove it. A Mandelbrot set should be displayed on the screen with some text stating it is Unified iBugger loader v0.1.1 running on Nano 4G.
To run emBIOS (which is most certainly what you want) run these commands:
python ibugger.py upload 08000000 embios-ipodnano4g-rXYZ.bin python ibugger.py execute 08000000 0a000000
You can then use the emBIOS tools to communicate with emBIOS
Helpful pages
Teardowns:
Other: